The Cutting Edge of Medical Technology Content, Community & Collaboration
Data breaches, malware and related frauds can cost an organization very dearly. The effects of cyber fraud are rather alarming:
It was estimated that cyberattacks amounted to a loss of at least a trillion dollars to the US economy in 2013, up by more than 25% over the previous year. The US continues to be the largest target and sufferer of cyberattacks. It accounts for more than a third of all cyberattacks that happen all around the world, followed by India, which is a distant second, at a ninth of that of the US.
 https://compliance4all14.files.wordpress.com/2017/07/security.jpg?w=150 150w" sizes="(max-width: 300px) 100vw, 300px" />
https://compliance4all14.files.wordpress.com/2017/07/security.jpg?w=150 150w" sizes="(max-width: 300px) 100vw, 300px" />
In terms of numbers of cyber attackers, the top cyber attackers are found predominantly in the developed world, with three of the top countries for cyber attackers belonging to the west. Germany is home to over a million cyber attackers, followed closely by the US, which had close to a million attackers in late 2013, followed by Mongolia and France.
A huge variety of losses
In addition to the financial loss that organizations face in the aftermath of a cyberattack, they have to also contend with other losses that are of a grave nature. Organizations in which fraud happens risk their reputation. They go down in the market as being run by incompetent and untrustworthy people at the top. Deloitte lists a number of other losses, both hidden and overt, that cyberattacks cause to organizations. These are some of them:
- Inability to meet regulatory compliance and having to pay fines levied by regulatory agencies
- Payment of losses and fees spent on litigation
- Costs relating to taking measures to improve security
- Cost of the investigation
- Loss caused by disruption to business
- Loss of intellectual property
- Increased cost of insurance
 https://compliance4all14.files.wordpress.com/2017/07/dollarphotoclub_64869762_2-1438304252.jpg?w=612&h=536 612w, https://compliance4all14.files.wordpress.com/2017/07/dollarphotoclu... 150w, https://compliance4all14.files.wordpress.com/2017/07/dollarphotoclu... 300w" sizes="(max-width: 306px) 100vw, 306px" width="306" height="268" />
https://compliance4all14.files.wordpress.com/2017/07/dollarphotoclub_64869762_2-1438304252.jpg?w=612&h=536 612w, https://compliance4all14.files.wordpress.com/2017/07/dollarphotoclu... 150w, https://compliance4all14.files.wordpress.com/2017/07/dollarphotoclu... 300w" sizes="(max-width: 306px) 100vw, 306px" width="306" height="268" />
What can be done about this?
If organizations need to prevent negative scenarios such as these; they have to implement a number of security measures and procedures. These security measures need to be in the form of an Incident Response Program that will allow organizations the ability to respond to such attacks with dexterity, while at the same time making sure that their business operations do not get disrupted.
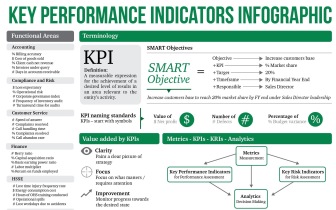
This calls for establishing Key Performance Indicators (KPI) to help to determine if organizations’ Information Systems Incident Response program meets business objectives and operational metrics for ongoing process improvement.
 https://compliance4all14.files.wordpress.com/2017/07/kpi_infographic_1_2.jpg?w=670&h=420 670w, https://compliance4all14.files.wordpress.com/2017/07/kpi_infographi... 150w, https://compliance4all14.files.wordpress.com/2017/07/kpi_infographi... 300w" sizes="(max-width: 336px) 100vw, 336px" width="336" height="210" />
https://compliance4all14.files.wordpress.com/2017/07/kpi_infographic_1_2.jpg?w=670&h=420 670w, https://compliance4all14.files.wordpress.com/2017/07/kpi_infographi... 150w, https://compliance4all14.files.wordpress.com/2017/07/kpi_infographi... 300w" sizes="(max-width: 336px) 100vw, 336px" width="336" height="210" />
Get to understand the ways of implementing cyber security
The ways of putting such a system in place will be the learning a webinar from Compliance4All, a leading provider of professional trainings for all the areas of regulatory compliance. Michael Redmond Consultant, a well-known speaker and author who also conducts ISO Certification Training for PECB, will be the speaker at this webinar. Michael is the Chapter President for Association of Contingency Planners Eastern Great Lake Chapter and an active member of ISSA.
Please log in to Business Continuity Planning to register for this webinar.
The key learning imparted by this training session is the ways of creating, testing and implementing an effective cyber Incident program to counter cyber threat and malware attacks. It will explain how to measure an organization’s susceptibility to a cyberattack. The speaker will explain the critical action areas in such events.
Ms. Redmond will explain all the measures that organizations need to take in order to avert a cyberattack, during the course of which she will discuss the following:
- How to tailor and enhance an existing security training program and set up requirements for specific audiences
- How to strengthen IT Risk Management – Integrate Information Security risk management with enterprise risk management
- How to build an IS regulation review process, schedule and regulation requirements
This session will be of high value to those professionals who are at the forefront of security operations, such as Information Security Managers, CEO, CIO, CFO, CSO, Technology Managers, Risk Managers, Compliance Managers, and Auditors.
The speaker will cover the following areas at this webinar:
- Adopting a systematic approach to risk tracking to enhance the effectiveness of the Cyber Incident Program
- Outlining the critical actions to take if an event affects the company or its partners
- Understanding an organizations’ susceptibility to a Cyber Attack
- Cyber Incident Response: Getting started, research, training, testing and maintaining
- Standards and Best Practice: ISO 27001, ISO 27035, ISO 27005. NIST, FFIEC, HIPPA and HITRUST.
Views: 18
Comment
© 2024 Created by CC-Conrad Clyburn-MedForeSight.
Powered by
![]()
You need to be a member of MedTech I.Q. to add comments!
Join MedTech I.Q.